Why Too Long Passwords Won't Boost Your Security
How long should your online password be to get the maximum security possible? This article analyses this problem from a mathematical perspective.
First of all, let’s analyze that characters that are used for a password and can be typed on the keyboard range from decimal values 32 to 126 on the ASCII table.
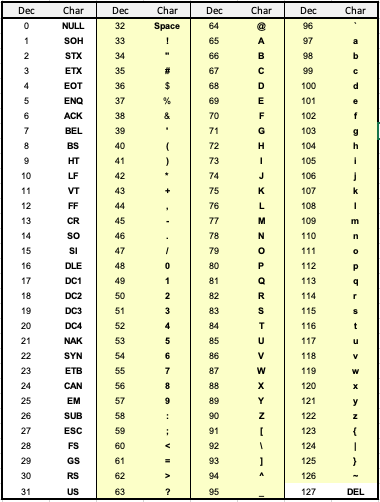
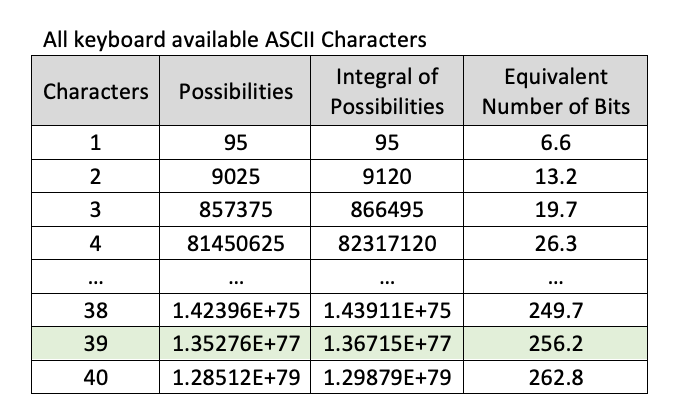
For a single character, I have 95 possibilities (126 - 31). To guess a one-character long password, you need to try guessing it at most 95 different times. Pretty simple.
Let’s calculate how many bits 95 possibilities correspond to. That is something between 6 and 7 bits, or to be exact 6.57 equivalent bits.

Note: to avoid any confusion, I will be using a term “equivalent number of bits” from a complexity perspective. This doesn’t mean at all that the password ASCII string will result in having that number of bits.
For example: an ASCII string “aaa” has 3 characters, and each character is 8 bits. That technically results in a 24-bit ASCII string, but I am not interested in this because, from a complexity perspective, I am after the number of possible values that these characters can be. The number of possible values dictates the complexity of the password. In this example, my equivalent number of bits is 19.7 bits. Of course, bits cannot be fractional, but this is just a complexity indicator. A detailed calculation is outlined further in the article.
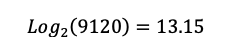
For 2 characters, I have 9025 possibilities (95 x 95 = 9025). If I know that my password is two characters long, it will take me at most 9025 trials to guess the password, and if I don’t know that my password is two characters long, it will take me at most 9120 trials (9025 + 95 = 9120) because I first need to iterate through 1-character long possibilities, and then iterate through 2-character possibilities. The equivalent number of bits will be 13.15.
Now let’s create a table and fill it out.
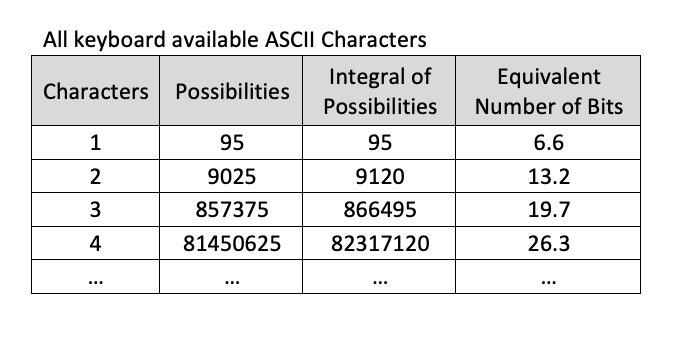
Bitcoin network uses 256-bit keys. To get an equivalent of 256-bit grade password, i.e. a saturation point, you would need to have 39 characters that include:
- 0-9
- A-Z
- a-z
- !”#$%&’()*+,-./:; <=>?@[]^_`{|}~
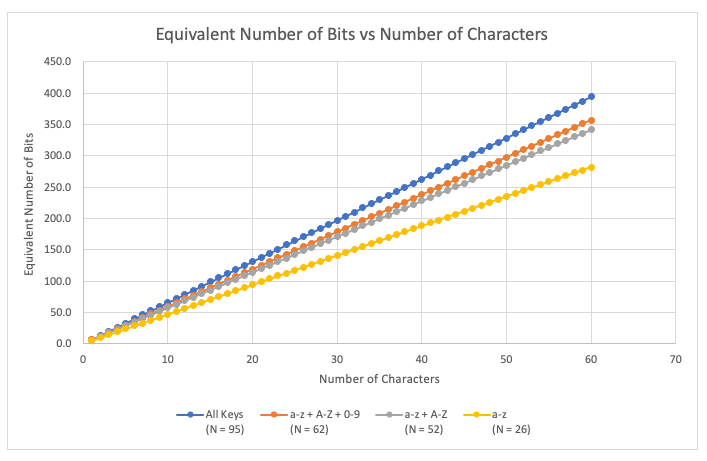
Let’s plot the graph. We see that for every additional character, I have a linear increase in the number of equivalent bits.
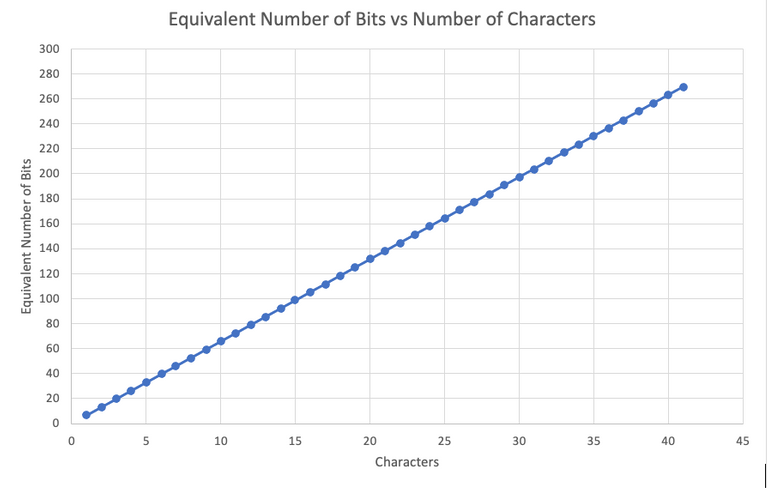
A password can have different types of characters, and that will impact the saturation point:
- Saturation length = 55, for characters a-z
- Saturation length = 45, for characters A-Z, a-z
- Saturation length = 43, for characters A-Z, a-z, 0-9
- Saturation length = 39, for characters A-Z, a-z, 0-9, !”#$%&’()*+,-./:; <=>?@[]^_`{|}~
Let's plot all these data points on the graph. The larger the slope, the higher the complexity of the password. The slope depends on the type of characters used in the password.
Does having an extremely long password make it more secure?
Intuitively, you may think that generating a password with over a hundred characters will make the password more secure, but would it? The short answer is not necessarily because it depends on what bit size is used in the hashing algorithm on the server backend.
There is no point in having a password with a greater equivalent number of bits than 256.
- First, it is already virtually impossible to brute force this number. That’s precisely why Bitcoin network is so secure with its 256-bit keys.
- Second, almost all passwords get passed through a SHA256 hashing function (or equivalent), which outputs a 256-bit value anyway. Therefore if you are hashing a value with more bits than 256, the hashed output will be limited to 256 bits, and you will not be gaining any additional security. Note that the hashing function generally gives a uniform frequency distribution.
- For example:
- On average, for each possible value of the 256-bit hashed output value, there can be 2 values of 257-bit input value (2^(256) x 2^1 = 2^257).
- And correspondently, there should be on average 4 values of 258-bit input values for each 256-bit of hashed output value (2^256 x 2^2 = 2^258). And so on.
It is highly recommended to use a password manager such as 1Password or Bitwarden to generate these long passwords automatically and insert them when you need to log in somewhere.
Since a 32-character string will technically be composed of 256 actual bits (8 actual bits per character), wouldn't anything greater than 32 characters make SHA256 output repeat itself? Technically it could, but a 32-character string has a limited number of possibilities because not all ASCII characters are utilized i.e. you only have 95 real character values out of 255 in a single byte (see the first table). So in the event of repeating, there is more probability that it will overlap with some value of a hidden character (not accessible on the keyboard) than a real combination of keyboard characters.
Would it hurt to have a long password that may cause the SHA256 output to repeat itself? No, it wouldn't hurt, but it wouldn't help eatiher. The output of SHA256 is uniformly randomly distributed, so even if there is a repeated output, the probability of such output matching to a hash of something simple as "123" equals to the probability of you guessing Satoshi Nakamoto's private key i.e. virtually zero. Therefore if you have an extremely long password, you are still fine.
Also, remember, no matter how secure your password is, the system may still be compromised. Your password may get leaked. So, make sure to have Two-Factor Authentication (2FA) enabled wherever possible. You can think of a password as a layer of protection, and you want to make that layer as strong as possible, yet you should still pay attention to other layers of protection.
Conclusion:
- Maximum password security level will be achieved with an equivalent number of bits of 256 from a complexity perspective (given the server uses a 256-bit hashing algorithm on their backend).
- For maximum password security level you should have 39-55 characters long password:
- Length = 55, for characters a-z
- Length = 45, for characters A-Z, a-z
- Length = 43, for characters A-Z, a-z, 0-9
- Length = 39, for characters A-Z, a-z, 0-9, !”#$%&’()*+,-./:; <=>?@[]^_`{|}~
- Having more characters than stipulated above, will not produce extra security (given the server uses a 256-bit hashing algorithm on their backend).
- Use a password manager to generate random values for the password. Let the password manager insert the passwords for you automatically.
- Maximum security level password doesn’t guarantee you won’t get hacked. Always have 2FA where possible.
#password #2fa #authentication #crypto #cryptography #bitcoin #crypto #databreach #stophacker #tips #math #tips #stophacker #encryption #hash #sha256 #secure #security #secure #cybersecurityawareness #hacks #hacker #hacking #bruteforce #statistics #email #passwordmanager #explained #tech #technology #datasecurity #business #info #dataprotection #cyberattack #key #privatekey

Great article. I myself have written a series of articles about password theory (among which Dispelling modern myths about passwords and How hackers are cracking your passwords) and also explained the origin of common bad practices in choosing password (Your insecure passwords and where to find them) and your article gives a proper and detailed insight on yet another side of this fascinating matter.
Congratulations @vasiliyxx! You have completed the following achievement on the Hive blockchain and have been rewarded with new badge(s) :
Your next target is to reach 50 upvotes.
You can view your badges on your board and compare yourself to others in the Ranking
If you no longer want to receive notifications, reply to this comment with the word
STOPI think instead of using very long password using different combinations altogether is something that makes password more secure. Creating a common password is never a good afterall.
Correct, that's why it's advised to use a password manager. You shouldn't be typing or even knowing what the password is; let the password manager handle that for you on your mobile device or computer. It's advised to create a list of websites that are the most important to you and upgrade the passwords there. This step is relatively easy when you have a password manager setup.