Post Firewall install check up

You got your new firewall installed and you want to play some Hunt: Showdown. Before you do, I recommend making sure you got everything working well and secure.
My previous post I talked about replacing my Edge Router with an OPNSense firewall. This was a massive upgrade as the hardware is a full blown PC allowing me to do a lot more at the firewall level than I could do before.
That being said, I keep my firewall locked down and I do not port foward to internal machines, I used to ages ago but I keep everything hosted off my network these days. Reguardless, you should always check to make sure your network is not exposing anything.
I'm going to go over a few checks you can use to make sure your network is locked down. Even if you didn't recently install a new firewall, these steps are a very good exercise to make sure you are not exposing anything unexpected.
There are two things in my experience people tend to ignore, backups and security. Both are extremely critical and can drastically affect your life if they go wrong.
Let's go over a few steps to do a sanity check on your network exposure.
Shields Up!
The first test I recommend you do is Shields Up! This is a relatively old service run by a well known Security Expert Steve Gibson.
The test is very simple to run and will allow you to see if you are exposing any ports.
All you need to do is hist proceed here.
At this point you want to select "All Service Ports" in the middle.
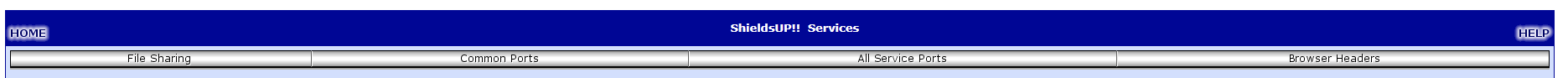
You should then see it going through all ports for your IP and when complete will tell you if you have any exposed ports. This test will only look at the first 1056 ports which account for a lot of the common services. It does not cover all possible ports though. There are a total of 65,535 potential open ports both TCP and UDP. This test only checks for the first 1,056 TCP ports.
The best case scenerio of this test is all ports are stealth as you can see from the results below.
Your system has achieved a perfect "TruStealth" rating. Not a single packet — solicited or otherwise — was received from your system as a result of our security probing tests. Your system ignored and refused to reply to repeated Pings (ICMP Echo Requests). From the standpoint of the passing probes of any hacker, this machine does not exist on the Internet. Some questionable personal security systems expose their users by attempting to "counter-probe the prober", thus revealing themselves. But your system wisely remained silent in every way. Very nice.
While we got a perfect result from this test, it is not a conclusive test for total security.
Shodan Scan
Next I recommend running a Shodan scan, Shodan is a search engine for finding exposed devices on the Internet. The test is really easy, just enter your public IP in the search engine and if it knows of any devices it will let you know. You do not need to sign up for an account.
A perfect result will be "No results found", this means it has no knowledge of any exposed devices or ports on your IP.
Censys
The next test I recommend running is Censys, another service very similar to Shodan.
Just enter your IP and you are looking for the following ideal results, like Shodan, you do not need an account.
If you received "no publicly accessible services" you are looking pretty good.
While this isn't an exhaustive test of your external security, it will catch the most common issues. I would recommend doing a full port scan of all 65,535 ports for both TCP and UDP to have a complete view of any potentially opened ports. There are paid services that offer this but the popular tool nmap can do this for you as well.
You can download nmap and do a full portscan on your ip using nmap -p- YOUR IP.
Posted with STEMGeeks
Thank you :-)
Great security information, for sure if we want to protect digital assets and ourselves, a firewall is a first defense. We tend to think on security after somehting bad happens to us, while we should take preventive measures.
your security values are very good. But there is a crane to break every wall, but be careful
very good and useful guide. Special for smart home owners or owners of old weird printers :)
Edit: An raspberry pi can work as a firewall too right?
Wow, this is all really useful stuff! I've been looking into setting up a more sophisticated digital security system for my home now that I'm exploring blockchain offerings and considering smart home devices. Several of these will be particularly useful for that project!
!1UP
You have received a 1UP from @entrepidus!
@bee-curator, @pob-curator, @vyb-curatorAnd they will bring !PIZZA 🍕
Learn more about our delegation service to earn daily rewards. Join the family on Discord.
PIZZA Holders sent $PIZZA tips in this post's comments:
@curation-cartel(1/20) tipped @themarkymark (x1)
Join us in Discord!
I guess all this setting makes the security less expensive than paying a business to do it for you .
Seeing as I have been doing this since high school, I have no need for any help. In fact I had a computer company while in high school.