Building a new firewall

I've been wanting to do this for a while. I use a router as my firewall which while extremely secure gives me little functionality.
The main reasons I want to replace it are:
- Exceed 1Gbit WAN
- Better logging
- Better IPS
- WireGuard VPN
Some of these things my router can do, but they can be done better. Doing them while maintaining 1.2Gbps connection is another story as well.
There are a lot of options for protecting your networking. My goal is end up with a setup like this.
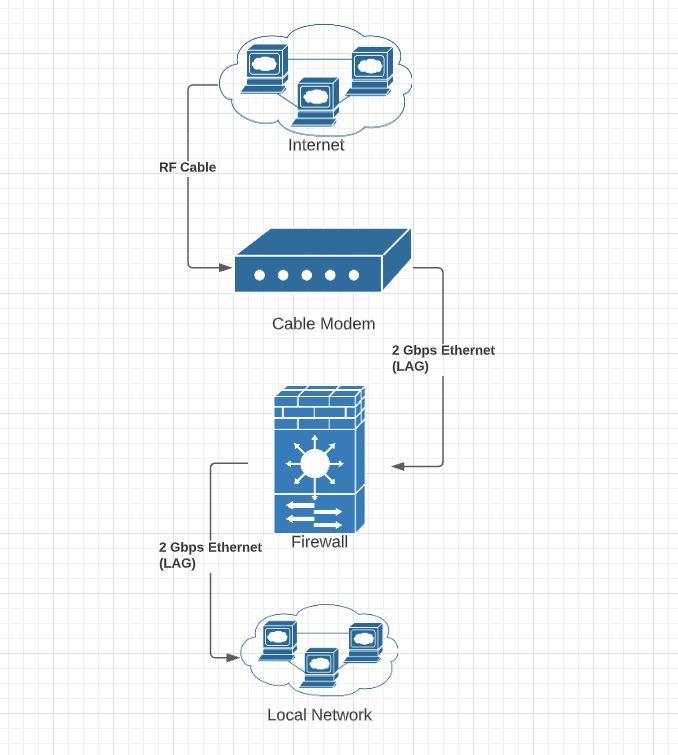
As I own my own cable modem, I am able to setup a LAG connection between it and my firewall. LAG (Link aggregation) simply is the ability to combine network cards to act as one connection. This allows me to break the 1Gbps limit of a single 1 Gbit Ethernet card. So in this diagram, the 2 Gbps Ethernet lines are two RJ45 cables between the cable modem and the firewall.
While LAG is great, it does not allow you to exceed the connection of a single network interface in a single connection and primarily benefits by supporting multiple 1Gbps transactions. Unless you use multiple connections at once, you will not see faster downloads, but multiple users will benefit from not being throttled at 1Gbps total connection speed.
The reason behind using LAG on the cable modem is the ability to take advantage of the full 1.2 Gbps connection offered by my ISP. I also need to provide a similar connection from the firewall to my local network to take advantage of this additional bandwidth. Two RJ45 Ethernet cables are connected from the firewall LAN ports to a 1 Gbps switch on my LAN.
I really wanted to go a 2.5 Gbps or 10 Gbps option for the firewall and cable modem to support potentially upgrading to 3 Gbps symetrical Internet but options are very limited without just using a full PC to handle it.
While 1.2 Gbps is enough for me even with my demanding needs, the upload is what sucks being only small fraction of the download. A symetrical connection gives me full speed in both directions and the only connection they offer that does this is their 3 Gbps in both directions. This would primarily help me with my offsite backup and moving large files between servers. Most activity wouldn't benefit from this at all.
So now that you have a gist of where I'm at, the next thing is to decide on hardware. I spent some time thinking about this and I really wanted to go with something that can support 3 Gbps if I went down that route. I also wanted to keep a small form factor device that didn't need fans allowing me to have a quite low power device.
Protectli provides high speed devices with lots of internal ethernet connections while being low power and heat sink cooled only.


I went with Intel i7 6 Ethernet Port option which is powered by an i7 8550-U processor.
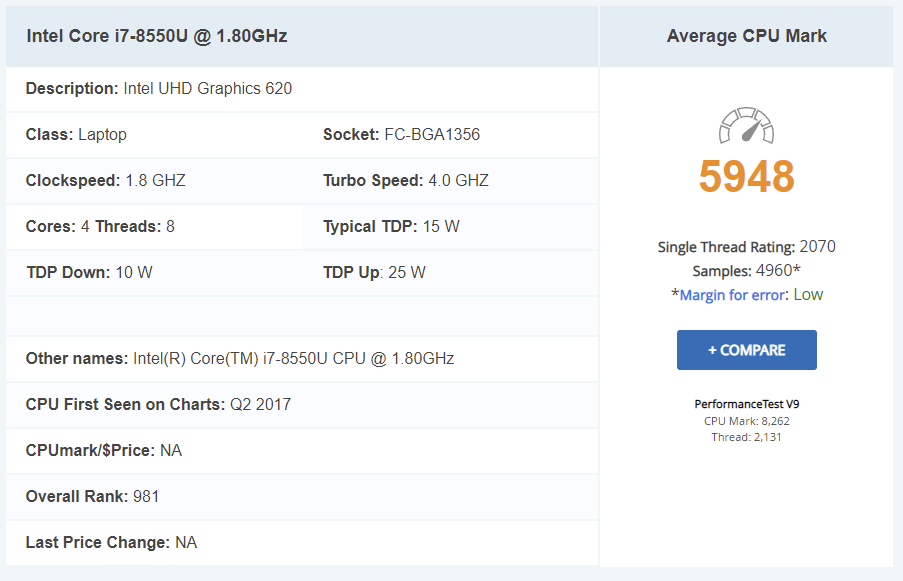
While not the fastest i7 out there, it is extremely fast for a firewall device and something of this size. It will handle what I need with ease with plenty of room to spare.
These devices have everything you need and are pre-built, all you need to add is ram and storage. I opted for the overkill option of 16 Gb of ram and 240 Gb of storage. The price difference between the recommended 8 GB and 120 G is small.
The total price for this set up is $859, a lot more than I really wanted to spend on a firewall but this will last me for some time and allow for much more control and security. To put things in perspective, my current Edge Router cost me $179, and while it works well, Ubuiti is going to shit and configuration is a nightmware and features are very limited. In fact, the direction Ubuiti is going, they are actually removing features in firmware updates.

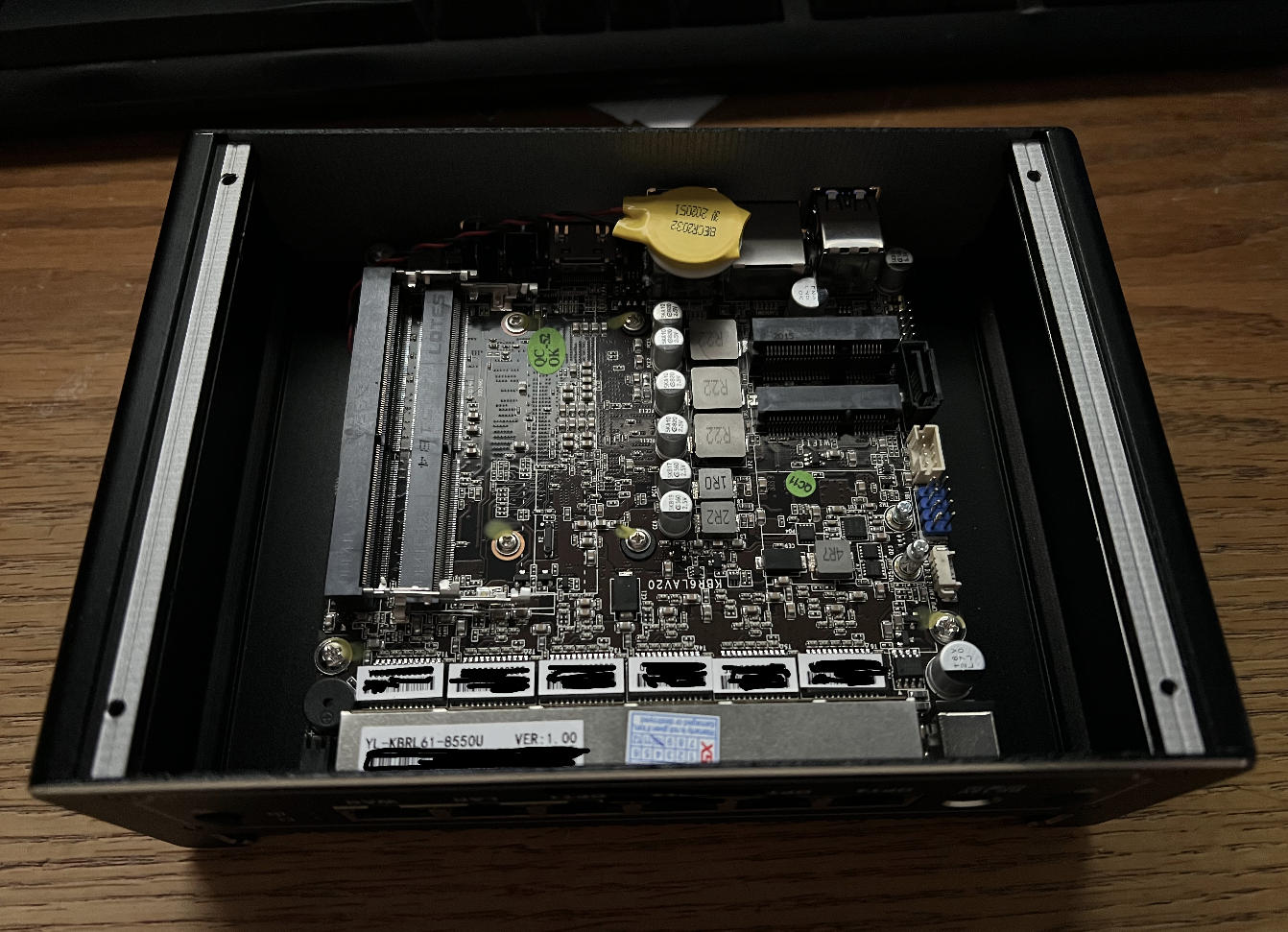
I purchased 16 GB of ram and a 240 Gb SSD drive separately, so I need to install these myself. This is as simple as removing four screws on the bottom and sliding them place.
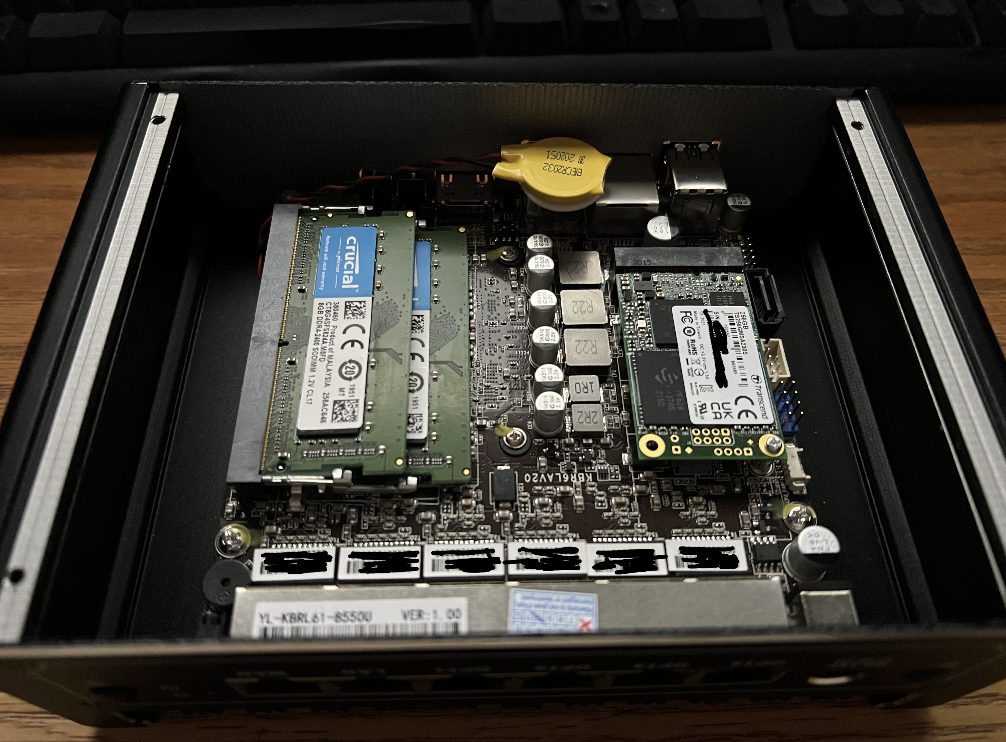
With that done, I just screw the case in and setup a USB stick for the software installation.
Here is the biggest advantage of using something like a Protectli device, you can choose what you want to install.
There are really three primary options out there:
- PFSense
- OPNSense
- Untangled
For me it was really down to PFSense & OPNSense as I wanted something built on open source software and not locked into a proprietary system like Untangled. Untangled is also $150/year, where both PFSense & OPNSense are completely free unless you want additional support.
OPNSense is a fork of PFSense so both solutions are very similar in the end. The main difference is what features they choose to add going forward, addon plugin support, and UI differences.
I opted to go with OPNSense as it tends to get newer features faster and has some other features that I feel make it a better option. Both solutions are great though and neither are a bad choice. There are issues in my opinion with the team behind PFSense which resulted in the OPNSense fork in the first place.
After downloading OPNSense and installing the VGA version to a USB drive, I was able to plug it in and start the install. The install is super simple and you just answer a couple questions, with the only real choice is if you want UFS or ZFS for your file system. I chose ZFS despite only having a single disk in the machine, ZFS is far more tolerant to sudden power failures.
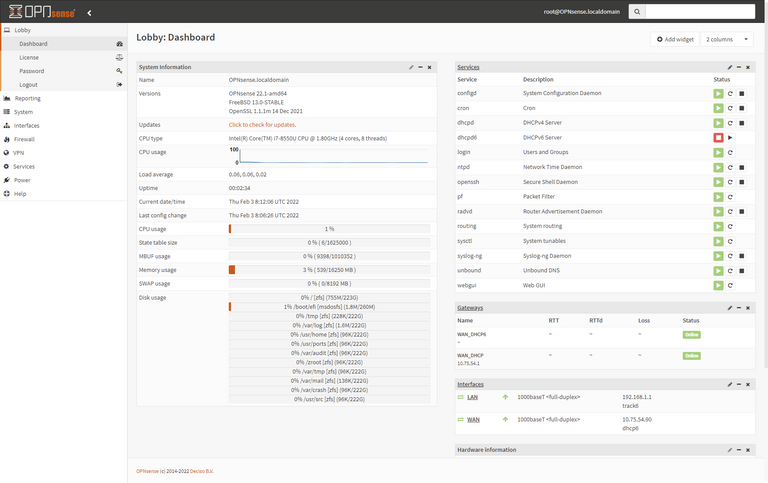
After the install and reboot I am into the OPNSense interface. Configuring this beast will take some time, but I need to initially setup my interfaces and set up LAG. I will use 2 interfaces for the WAN and 2 for the LAN leaving 2 interfaces for a DMZ. A DMZ is a subnetwork that isn't really on the WAN and isn't really on your LAN either. This provides more security than a port forward to your internal network. I don't host anything off my LAN these days so I won't likely use this feature, but it is there if I want to down the road. Due to security and potential power outages in snow storms, I stopped hosting exposing my network to anything many years ago.
Once I configure interfaces and LAG, I pretty much can just swap out my router for this as everything should work at that point. I will however do some looking around learning the features and setup Intrusion Protection Services (IPS) and some other features before moving things over.
While I said before multiple interfaces won't provide a single connection improved performance, a lot of the most bandwidth critical services I use (downloading and off-site backups) support multiple connections allowing them to go past the 1 Gbps limitations of a single network card. This will allow me to take advantage of the 25% additional bandwidth I now have with two NICs.
Posted with STEMGeeks
Wow,this sounds so good and nice to see those improvement you tend to see after having those development
I really which to learn more from you, it's really an amazing thing to engage on
This was so much fun to read! Thanks for taking the time to post it!
This is the WAY!!!
I love theses articles you write, sadly very infrequently! The thing with firewalls though is that many people possibly don;t realise, they aren't going to protect you from viruses and worms etc and that anti-virus software is still needed.
You're a professional IT security guy, what advice do you have for us home users on anti-virus software and any 'insider tips' on how we mainly WIndows and Mac users should be protecting ourselves.
Thanks in advance and have a great weekend :-)
I personally recommend Kaspersky & Bit Defender.
I recommend checking out the independent reports here:
https://www.av-comparatives.org/
I would recommend looking at multiple reports (there are different classifications) before making a decision.
I have been in the information security industry most of my life.