Bridgefy: a network-less messaging app that is an unmitigated security disaster

Do you remember toothing? It was a spectacular prank perpetrated around 2004 on the media who reported it, according to which Bluetooth-enabled devices were used to arrange random sexual encounters. What made it special was that, unlike any generic hoax, the technical foundation for toothing was sound: due to Bluetooth operation modes commonly implemented at the time on mobile phones and PDAs (which were designed to share address book entries and other basic information between devices) there actually was the possibility of sending messages to a perfect stranger within Bluetooth range, albeit in a crude form, or giving your device a specific Bluetooth ID (like "toothing?" or similar) that would be automatically visible to all other nearby devices, in the hoax narrative, to indicate interest. The most hilarious part of this story is that, while the pranksters only wanted to "highlight how journalists are happy to believe something is true without necessarily checking the facts", the widespread press coverage coupled with its technical feasibility made toothing actually happen: "Multiple forums were in fact created throughout Europe, Asia and America within months of the original post of toothing. People signed up to the forums looking for good locations in their area to tooth, and to share their toothing stories with other members." (source: Wikipedia)
Fast forward fifteen years later and enter startup company Bridgefy: their main product is an SDK, implemented in a messaging app available for iOS and Android, and designed to "make mobile apps work using mesh networks instead of Internet, letting your users engage with your app during large events, natural disasters, schools, and much more". Sounds familiar? Yeah, it's basically toothing on steroids, structured in a mesh network to extend the range and enable device-to-device communication in absence of mobile or Wi-Fi network. In the intent of its developers, this would be the solution for establishing a local, reliable communication system when standard connectivity is for any reason failing or unreliable. Anyone who has tried to communicate using a mobile phone from a concert knows that mobile networks can struggle due to congestion, and even with the best intentions a mobile operator is helpless against the disruption brought by flooding and other disasters.
In these scenarios, a distributed mesh network that relies on Bluetooth for near-field communication (where each device has a range between 25 and 100 meters) may represent a good idea to relay messages, as node density becomes a positive factor rather than causing congestion.
All would be good and well, except that - in coincidence with the recent years surge in political protests and riots around the world - Bridgefy started heavily advertising on interviews and media outlets that the app featured end-to-end encryption ("except broadcast chat messages"), implicitly suggesting that it would provide a reliable, internet-independent and safe communication channel against censorship (sources: Forbes, 3nions, Ejinsight).
The company pushed the envelope even further, even promoting the app directly to activists and extending reassuring messages about privacy commitment and lack of political affiliation (source: Twitter).
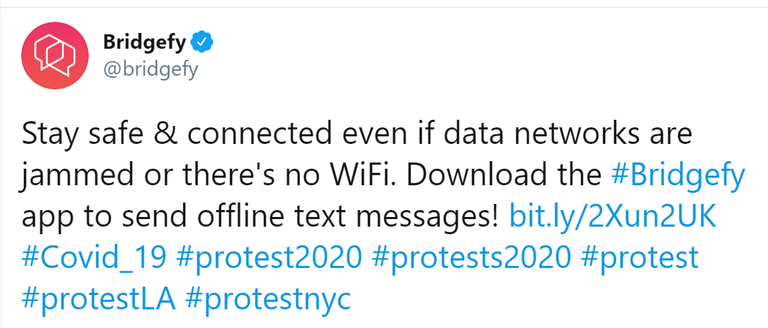
(source: Twitter)
Except that, of course, almost none of that was true.
Security is not invented overnight
In a paper published by the University of London (source) a team of researchers led by Martin Albrecht has disclosed how almost all the privacy and security features advertised by Bridgefy about their app are inaccurate, misleading, or implemented so poorly as to become ineffective. As a matter of fact, upon reverse engineering, the app has been found vulnerable to an impressive series of attacks which can successfully lead to:
- loss of anonymity
- decryption of direct messages
- man-in-the-middle attacks which allow to read messages and tamper with them
- arbitrary user impersonation
- construction of social graphs including users interactions (after the fact and in real-time)
- complete network shutdown by Denial of Service (with a malicious payload).
This was made possible due to a remarkable number of oversights in the implementation of basic security protocols and best practices inside the Bridgefy SDK:
- lack of cryptographic authentication (each user ID is sent in plaintext) which allows spoofing and MitM attacks
- RSA encryption based on PKCS #1, an encoding method deprecated in 1998 that allows attackers to perform a padding oracle attack to obtain the contents of an encrypted message
- lack of protection against topology mapping (as both sender and received ID are included in plaintext)
- lack of input sanitization and buffer control (which allows an adversary to broadcast a malicious packet that will overflow and crash the app on any receiver device).
The app will improve... eventually
Following the responsible disclosure of the researchers' findings in April 2020, Bridgefy has started issuing corrections to their previous statements to highlight how the app does actually not provide end-to-end encryption and its encryption system design has been found to be unsafe, and therefore removed altogether. The company then published a statement acknowledging the flaws listed in the research paper and announcing that the SDK is undergoing a major overhaul of the security layer that will be based on the Signal protocol (a standard, open-source cryptographic protocol that is known to provide a high level of security and robustness, implemented in several messaging apps such as WhatsApp, Facebook Messenger, and Skype).
From a security expert's point of view, this blunder is entirely self-inflicted and results from the compounding of two capital sins:
- the Bridgefy SDK was never designed for usage in adversarial conditions (riots, protests) where an external agent (be it a security agency, or the police, or a repressive government) has an active stake in intercepting, compromising and disrupting the network
- Bridgefy grossly misrepresented its software capabilities by actively advertising it for usage in contexts that were outside of its scope.
Cryptography is a mature science with a solid foundation of algorithms, guidelines and best practices that have been developed in the past decades to provide reliability, robustness and security. It is also unforgiving, as any deviation from best practices will invariably result in vulnerabilities and flaws that are well known and documented. It is not difficult to correctly implement a cryptographic system, but it cannot be improvised or negligently executed.
While it is commendable that Bridgefy has acknowledged their mistakes and started working to amend them, such a glaring collection of missteps and oversights cannot be discounted, and should recommend - from now on - avoiding their products entirely.
Congratulations @lucabarbera! You have completed the following achievement on the Hive blockchain and have been rewarded with new badge(s) :
You can view your badges on your board And compare to others on the Ranking
If you no longer want to receive notifications, reply to this comment with the word
STOPTo support your work, I also upvoted your post!
Do not miss the last post from @hivebuzz:
@tipu curate 2
Upvoted 👌 (Mana: 0/45)
Solid read @lucabarbera
Resteemed already. Upvote on the way :)
an interesting concept indeed or shall I say a work in progress
good luck with your research and postings @lucabarbera
Thank you! I believe that Bridgefy will come back with the updated version of their app, but the PR damage is severe and many will simply not trust them anymore.