Cryptography And Blockchain Explained Easy
The Crypto Side Of Currency
We all talk about cryptocurrencies or crypto. Here are briefly explained the concepts of cryptography and blockchain. Simplifications and omissions are voluntary.
Cryptography
Cryptography is the protection of messages using a secret key. This ensures the confidentiality, authenticity and integrity of the message. Only authorized people (having a key) can read it, authenticate the sender and verify that the message has not been modified.
The need for confidentiality and authenticity of communications is no longer to be demonstrated. We all use encryption when we surf the web.
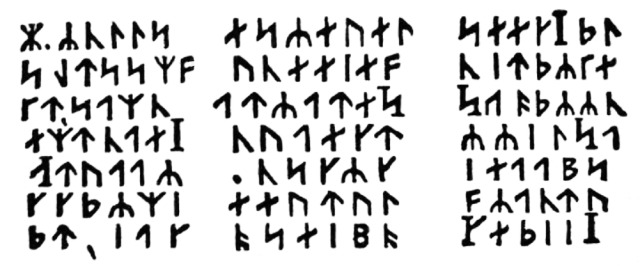
The Cryptogram of Jules Vernes
Source: J. R. R. Tolkien's influences
Encoding
Encoding is not encryption but a conversion following a rule or correspondence table. The bits in a computer's memory are numbers representing the characters that make up our sentences. The correspondence depends on the encoding used.
Character encodings are for example UTF-8, ISO-Latin-1 or Unicode. Base 64 is used to encode binary for a text interface, eg an inline image. Spaces in internet addresses are URL encoded.
Hashing
Hashing is a mathematical function that reduces data to a large number, the hash. If the data is identical the hash is the same, if it changes by one bit the hash is not close but completely different. A hash is typically written with hexadecimal digits (eg d41d8cd98f00b204e9800998ecf8427e).
Hashing is very useful. If a site displays the hash, you can verify that the downloaded file is not corrupt. They allow you to compare remote files by only passing their hashes and not their content. They have many other uses, such as indexing and especially securing the blockchain.
Hashing algorithms are for example MD5 or SHA.
Key
The key, or secret, is derived from the password or the pass phrase. In the case of a wallet, the pass phrase is the 12 words used to generate the succession of addresses (of keys). A key cannot be memorized by a human being. In crypto, the keys are encoded in a format that makes it easier to write the key and import it into a wallet, by copying and pasting or scanning a QR code.
Encryption
Symmetrical
Symmetric encryption uses the same key to encrypt as it does to decrypt. It is used in protection by password.
Symmetric encryption algorithms are for example DES or AES.
Public-Key (Asymmetric)
Asymmetric encryption uses 2 keys, the private key and the corresponding public key. The private key must remain secret, the public key (derived from the private key) is published or transmitted to the correspondent authorized to read the message.
A message encrypted with the private key can be decrypted with the public key and conversely, a message encrypted with the public key can only be decrypted with the private key.
Asymmetric encryption algorithms are for example RSA or DSA
Signature
Message signing is the asymmetric encryption of the message with the signer's private key. The authenticity and integrity of the message can be verified with the corresponding public key.
Certificates
A certificate (known as SSL) is a kind of business card, signed by a certificate authority. The certificate can be verified with the public key of the certification authority.
Certificate authorities are for example GoDaddy, Comodo or SwissSign.
Salt
A salt is a small amount of data (a random number) added to the message before encrypting or hashing, to add entropy so that two same messages encrypted in the same way produce different data at each time.
This makes hacking more difficult therefore encryption more secure.
The Crypto
Blockchain
A blockchain is a register that contains all the transactions. The status (balance) of an address is determined by the succession of all transactions. Transactions are grouped into blocks and each block contains the hash of the previous block.
Bitcoin
Transactions (Bob sends 50 BTC to Alice) are messages signed with the private key of the address that sends (Bob). These transactions are collected or refused (when the balance is insufficient) by the nodes of the network and grouped in blocks. The hash of the previous block is added, the block is timestamped, signed and broadcasted to other nodes.
Everyone now knows that Bob owns 50 less BTC and Alice more.
The address is (linked to) the public key, eg 13rTZRC2ptZ87SEMogGPhUDGPpSmedMkiE.
The private key is the secret that allows the money to be spent by transferring it to another address. If the key is lost, the money will be permanently blocked.
An address and its private key (paper wallet) can be created securely at https://www.bitaddress.org/
Hive
In the Bitcoin blockchain only money transfers (with a memo) take place. In the Hive blockchain, there are also posts, comments, votes and even game moves!
A Hive address is simply the login without @, eg droida. The password is used to generate the private keys (posting, active, owner, memo).
The active key is used to transfer money. The posting key is used to post and vote.
The memo key is used to encrypt messages. The owner key allows you to change the password, taking this way ownership of the account.
More Information
https://en.wikipedia.org/wiki/Cryptography
https://bitcoin.org/bitcoin.pdf
Contest
10 HIVE to win for the first who finds what is the data hashed using MD5, used in the hashing example.
French version: @droida/la-cryptographie-et-la-blockchain-simplement
!BEER
View or trade
BEER.Hey @droida, here is a little bit of
BEERfrom @eii for you. Enjoy it!Learn how to earn FREE BEER each day by staking your
BEER.