StrandHogg Vulnerability - Phishing you on your Phone
A recently disclosed vulnerability dubbed "StrandHogg" has brought phishing to a new level. In most cases, phishing involves a simple ruse (usually through emails or SMSes) to trick you into clicking a malicious link or open a bad attachment. After being tricked, the victim then suffers the consequences as the malicious site attempts to steal his/her sensitive information or the attachment detonate and affects his/her computing device.

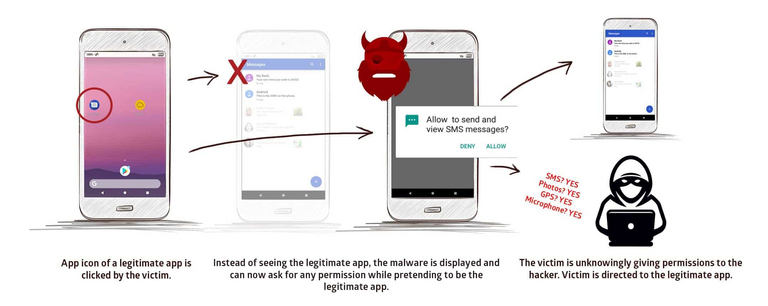
The newly discovered vulnerability by the researchers at Promon brings it to a different level as it allows a malicious app or malware to pose as legitimate apps, with users unaware they are being targeted. Here is a video of the vulnerability being exploited.
How does it work?
Based on the study from Promon, the malicious apps/malware has so far not been hosted on the Google Play store. This is because the malware might not pass the "Google Play Protect" scans especially when these apps are asking for highly sensitive permissions. Instead, these malware are typically dropped into the phone via dropper apps. Dropper apps are also malicious apps that are used to download and install malware silently. Such apps are more likely to pass Google Play screening as they do not require too sensitive permissions.
Once the malware is installed, it exploits the "StrandHogg" vulnerability which uses a weakness in the multitasking system of Android to enact powerful attacks that allows malicious apps to masquerade as any other app on the device. This exploit is based on an Android control setting called ‘taskAffinity’ which allows any app – including malicious ones – to freely assume any identity in the multitasking system they desire.
What makes this vulnerability highly dangerous is that it does not require "root" permission to exploit it. It is also found in all versions on Android and most if not all apps can be masqueraded using through this vulnerability.
Source

Source
What can I do to protect myself?
According to the researchers, Google has yet to patch this flaw in the 'taskAffinity' function. Hence, all Android users are still at risk. The best way to protect yourself is to be vigilant of the permissions that you grant to applications.
The key objective of malware exploiting this vulnerability is to phish you into granting the malware sensitive permissions. Such permissions may include, but not limited to:
- READ_CALENDAR
- WRITE_CALENDAR
- CAMERA
- READ_CONTACTS
- WRITE_CONTACTS
- GET_ACCOUNTS
- ACCESS_FINE_LOCATION
- ACCESS_COARSE_LOCATION
- RECORD_AUDIO
- READ_PHONE_STATE
- READ_PHONE_NUMBERS
- CALL_PHONE
- ANSWER_PHONE_CALLS
- READ_CALL_LOG
- WRITE_CALL_LOG
- ADD_VOICEMAIL
- USE_SIP
- PROCESS_OUTGOING_CALLS
- BODY_SENSORS
- SEND_SMS
- RECEIVE_SMS
- READ_SMS
- RECEIVE_WAP_PUSH
- RECEIVE_MMS
- READ_EXTERNAL_STORAGE
- WRITE_EXTERNAL_STORAGE
Having such permissions may allow the malware to perform the following sensitive activities:
- Listening to the user through the microphone
- Take photos through the camera
- Read and send SMS messages
- Make and/or record phone conversations
- Phish login credentials
- Get access to all private photos and files on the device
- Get location and GPS information
- Get access to the contacts list
- Access phone logs
Hence, we as users need to be mindful of the permissions that we grant to applications. If you downloaded a weather app, it typically should not need to send an SMS or access your contacts list. If an app is asking for something which you think is unnecessary, it is an immediate red flag.
Here is a quick tip, many apps will ask for permissions even though they do not really use them, even for legitimate apps. Even if you deny those permissions, chances are that the app will still be usable. For example, I have a shopping app called Lazada which keeps asking me for location access each time I launches it. I deny it every time and the app still works fine.
Conclusion
Security vulnerabilities get discovered on a daily basis. We as users of technologies are constantly exposed to such risks. The best way to mitigate them is to practice a little bit of skepticism. When you find that something is amiss, it likely is. Human intuition is often extraordinary. :)
10% of post rewards goes to @ph-fund and 5% goes to @steemstem to support these amazing projects.
This article is created on the Steem blockchain. Check this series of posts to learn more about writing on an immutable and censorship-resistant content platform:
- What is Steem? - My Interpretation
- Steem Thoughts - Traditional Apps vs Steem Apps
- Steem Thoughts - A Fat or Thin Protocol?
- Steem Thoughts - There is Inequitable Value Between Users and Apps
- Make my votes count! Use Dustsweeper!
- What caused STEEM to get dumped? Why I think the worst might be over
- Steem 2020 is about having a "SMART U"
Hello,
Your post has been manually curated by a @stem.curate curator.
We are dedicated to supporting great content, like yours on the STEMGeeks tribe.
If you like what we are doing, please show your support as well by following our Steem Auto curation trail.
Please join us on discord.
I always have to admit that the ability and creativity that we humans have to find ways to harm the lives of our fellows seems to have no limits.
Much progress has been made in the old days of hackers and phone phreaking, but even today the most vulnerable link in the security of a system is the users.
I would like protection systems to shortly identify those applications that drop accounts are loading our devices with malicious programs, but a part of my suspicion that the creators of these evil engenders will find some other way to bother us again.
That is true. Users are still the weakest link in many cases
This post is shared to Twitter,
https://twitter.com/CryptoCulgin/status/1203131545323655168?s=20
#posh #oc
This post received a 47% vote from @randowhale thanks to @culgin! All funds sent to @randowhale will be used to improve the SBD peg and will be burned at a later date.
Congrats! on your upvotes from the IBT Community
Greetings my friend @culgin.
The creators of malware and viruses do not rest in their work. Previously, computer viruses were developed with the idea of causing discomfort in the operation of operating systems and applications. Much has been said about virus developers, among other things that work as a production department for antivirus firms, who create the disease and then offer the cure.
Today, phishing goes beyond the purpose of viruses and malware. Theft of private information for extortion is one of them. But I think the main objective is to obtain information related to access codes to bank accounts and cryptowallets.
Thank you for sharing this valuable information.
Your friend, Juan.
You are welcome and thanks for reading!
Hi @culgin
Friend- I can only say:
Wow We are at the mercy of this type of attack and the worst part is that many people do not realize when they grant permits.
What great information you should also do in Spanish
Thanks! Unfortunately, I do not know Spanish. Feel free to translate it if you think it will benefit the Spanish readers 😉