My Second day of Ethical hacking

Yesterday I was exhausted so I didn’t had the energy to write my experiences of the second day of my course Ethical hacking. I will try to do that now :)
The second day was all about using the right tools for the job. And to accomplish that we had to follow a case. The case was about a company whose crown jewels is a recipe of their cola ;) .
All that we got was the IP address of the server where the web-environment was running, the rest was up to you. Like I mentioned in my previous post you have to think like a hacker to try and find some vulnerabilities.
Step one: Scanning

Source
When you have a IP address you firs can scan it to see which Information you can gather of the server. You can do this by hand or with tools.
For instance Dirbuster. Dirbuster is a tool which can discover content on a server or computer by testing folders and filenames and gives them back in a file or on screen. With that information you can try if you can enter the directories Dirbuster found.
With Dirbuster I discovered a directory “Intranet” and a directory “Intranet/Uploads”. So they had an intranet, how cool :)….
Step two: Vulnerabillity inventory
The next step was to look if the intranet was up and running, and it was….
So I connected to the intranet, using the url, and saw that it was an apache webserver.
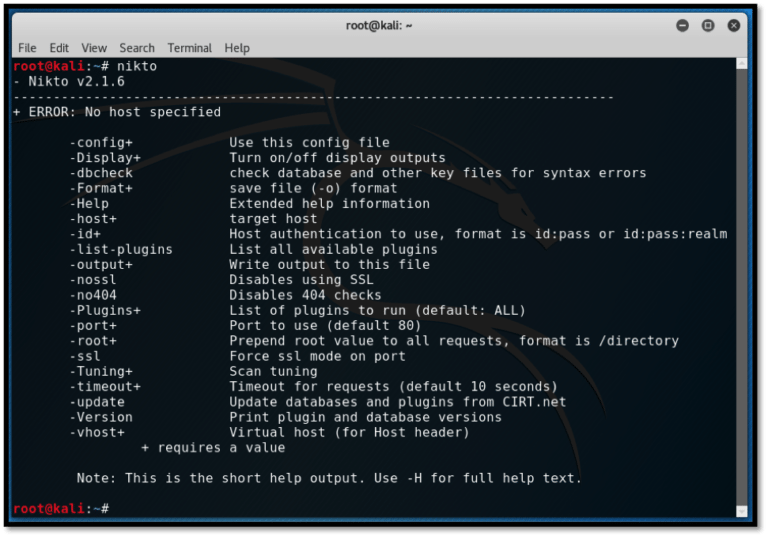
With tools like Nikto and Vega you can check vulnerabilities on a webserver. Vega gives a graphical view of the findings in terms of High, Medium and Low.
When you see high’s you know that that will be your point of interest to investigate further. :)
The webserver seemed to be vulnerable for SQL injection.
Step three: SQL Injection
SQL, Structured Query Language, is used to communicate with databases, and a lot of websites use databases to store or present data. With SQL injection you can manipulate the data towards the database and get some surprising results, for example:
- Revealing data that is not supposed to be seen by us
- Manipulation of data
- Removal of data
- Server takeover
- Find (login) details from clients or employees.
You can check if a parameter change works by trying it in the address bar of the browser.
Example:
Assume the address is http://webstore.com/index.php?p=content&pageid=1
You can try change the pageid to another number. is http://webstore.com/index.php?p=content&pageid=2
When you then hit enter maybe you will receive an error, from within that error you can investigate the system behind it…
So when you know that SQL injection is possible you can use a tool called SQLmap. This tool tries different kinds of injection on the server to reveal information and vulnerabilities.
For example:
- Enumerate all databases which are present on the server
- Get the passwords from the server and will ask you if the tool should try to crack them
- Will show all tables which are present in the database
- Dump all data from the databases in a file
- Gain access to the entire system from data which is in the database
- Testing to see if there are writable directories on the server and start operating system shell
Step four: Password cracking
When you get the passwords from out of the table you also can do a separate password crack attempt. With that you have multiple options but two common methods are:
- Dictionary based cracking: Based in a provided list of words. This is limited to the list of words.
- Brute force attack: Trying every possible combination of words.This can take very long.
A tool on Kali Linux which you can use for this is John the ripper.
For brute force there are multiple tools available like:
Aircrack-NG for Wifi
John the Ripper
L0pthCrack
THC Hydra
As you can see they all have exotic names :)
Alsost all websites work with parameters, not strange to think that these parameters can be manipulated in some way. Parameters work in general with Post and Get commands on the.
With the Get request you can read the parameters from an URL of command.
One tool to be able to manipulate parameters is Burp Suite. This tool works as a proxy server between your browser and the webserver so you can manipulate data. I thought that Burp Suite wasn;t that easy to use, a lot of options and dependencies, but the teacher showed us many possibilities of the tool… So try it sometimes, it’s free.
Parameters are also often stored in cookies. So cookies are a good place to manipulate parameters. Way back it was more common, lately only very bad programmed websites write parameters in a cookie.
The worst example is a cookie with the parameter “admin=false” . I don’t have to tell you what would be possible with that ;).
Step five: Dynamic file inclusion
One last technique to use is Dynamic File inclusion on a website. With this technique you use a vulnerability where you place a file on the server and execute it with malicious code.
As you can see you can use a whole set of tools to get eventually to your target with positive result. If you like this content you should have a look at Kali Linux , in this linux image all these tools are present. Just be aware not to use them in a real environment because it’s against the law :)
Well I hope you liked this post, I loved writing it and I am for sure continue with a lot more studying Ethical hacking,
Take care, stay safe,
Peter
I am with QURATOR, are You?

I am using Esteem


They are the creators of Steemify, THE notification app for your Steemit account for IOS.


Novacadian gives a tip of his white hat to @verhp11. 😎
thanks @novacadian :)
Wow, that is pretty awesome. I like how in depth they are getting into this for you. It is also really cool that you can do some real time tasks to apply the skills and tools that you are learning about. I might have to look for one of these types of classes close to me.
Awesome isn't it. I have really learned a lot, inlcuding my new course after this one... OSCP :) is more indepth, and a lab exam of 24 hours hahaha.... A realtime hack to be placed...
Very cool!
Thanks for mentioning eSteem app. Kindly join our Discord or Telegram channel for more benefits and offers on eSteem, don't miss our amazing updates.
Follow @esteemapp as well!
Such an interesting read, I am no expert in this area but know enough to be dangerous, but I have members in my team who use these or similar methods and tools when they conduct Vulnerability and security assessments
Thanks @tattoodjay , it indeed can be dangerous. Although nowadays a lot of sites and webapplications are pretty safe out of the box, it's the afterwork and customization which introduces some risks :)
yes indeed, we have many applications and sites that have customization or are built inhouse ( which slowly there are less of) and I have seen from the reports how those can be risky if not done well
Hi, @verhp11!
You just got a 2.32% upvote from SteemPlus!
To get higher upvotes, earn more SteemPlus Points (SPP). On your Steemit wallet, check your SPP balance and click on "How to earn SPP?" to find out all the ways to earn.
If you're not using SteemPlus yet, please check our last posts in here to see the many ways in which SteemPlus can improve your Steem experience on Steemit and Busy.
I used to be a pentester for a living. This is a pretty decent overview of how hacking usually works
Thank you @culgin , you're not working anymore in the field of Ethical hacking?
I now do more coordination of pentests and other security assessments. No longer doing field work. Haha..
Hi @verhp11!
Your post was upvoted by @steem-ua, new Steem dApp, using UserAuthority for algorithmic post curation!
Your UA account score is currently 3.504 which ranks you at #6938 across all Steem accounts.
Your rank has not changed in the last three days.
In our last Algorithmic Curation Round, consisting of 113 contributions, your post is ranked at #97.
Evaluation of your UA score:
Feel free to join our @steem-ua Discord server