Learning and Earning Cash From Doug's Stash
So this year, Santa looked a little bit different...

The other day I had happened to notice an interesting post by @themarkymark. Apparently @themarkymark had set up an alt account called @dougs-stash into which he deposited 100 Hive to be a reward for anyone that could find the key from solving a puzzle from clues found in the post. Of course there is nothing more the OldGuy likes better than free money and an interesting puzzle so I thought I would just sniff around a bit. I went for the low hanging fruit first and checked out social media for Doug Stash. There I I learned there is a YouTube video about Doug Blanchard/Stash. Well Doug Stash is on Facebook and has a pit-bull. Oh I almost forgot, Douglas Blanchard (his full name) sells some art on Fine Art America lol.
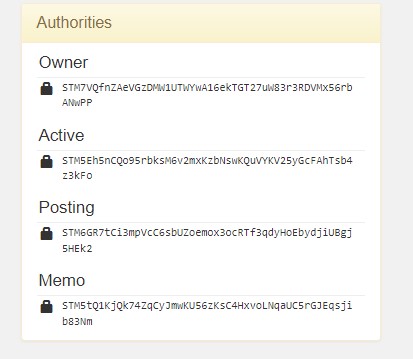
Well that was a dead end! So I thought I would google the public keys. Of course at the this time I had no idea how deep this would end up. You got to start somewhere and I thought this might do the trick... Ha not even close!
Enter the Cicada

Or more aptly Cicada 3301
So the OldGuy has never been the sharpest tack in the drawer, but it doesn't take me too long to realize when I am out of my depth. I know I needed help, but it is Christmas so who can I rope into helping me.... Oh well, yes of course, Ben, @benjamintaylor my son that I feed and that is studying computer science and needs cash as much as I do lol.... So I show him the post and he zeros in on:
Doug is a programmer and he knows all sorts of neat tricks to hide data where no one else can find it. He also knows all the protocols TCPIP, NFS, IPFS, UDP.
So Ben starts telling me of some bizarre happenings that started around 2012. A group called Cicada 3301 started posting these challenges that relied on cryptology and steganography to solve. Most of us know basically about what encryption is, while steganography is hiding data in pictures... BINGO!
There are not many obvious clues but there is this picture...

So let's have a look... Oh this is a clue alright! Look what the picture was named: "redherring" lol. Ok for someone to change the name to that, I knew we were on the right track!
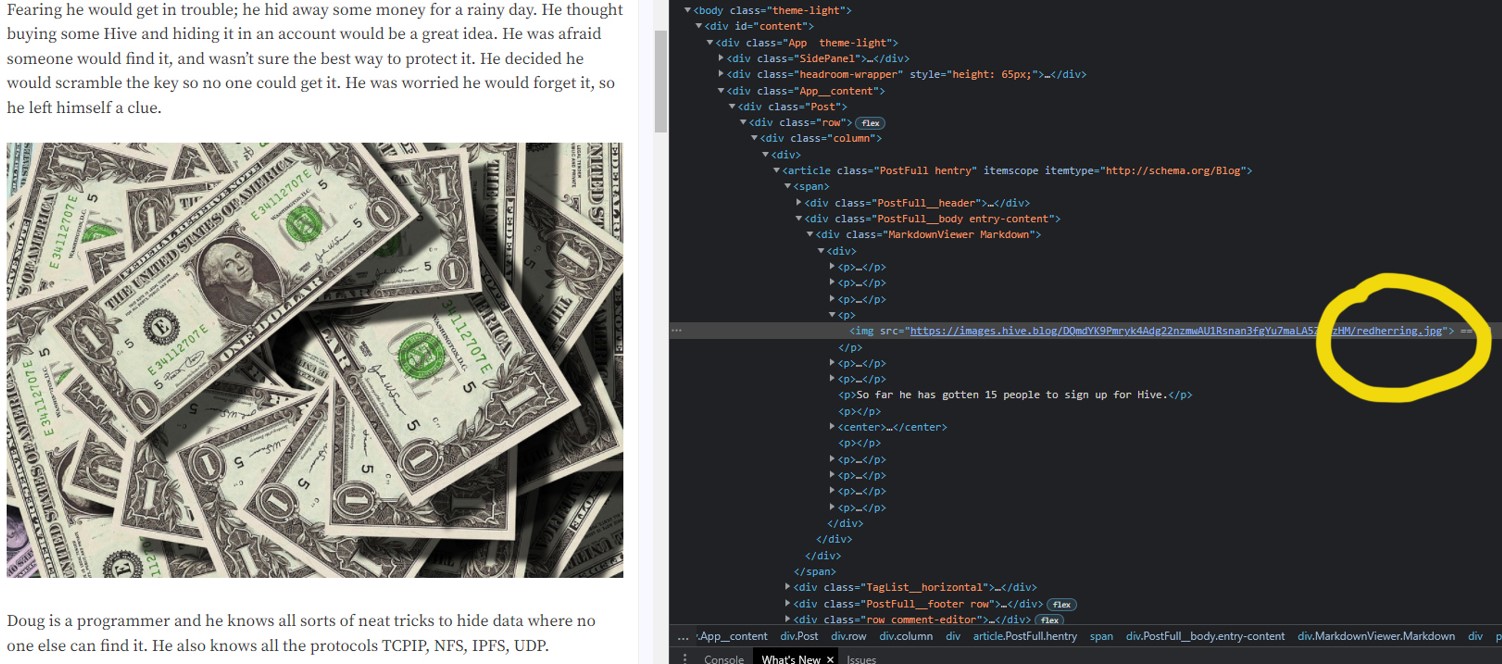
So if that was in fact a red herring, the next image to inspect was:
The Hive banner?!?!
.png)
Looking at the page source code we noticed that Hive blog pictures are hashed beginning with "DQm"
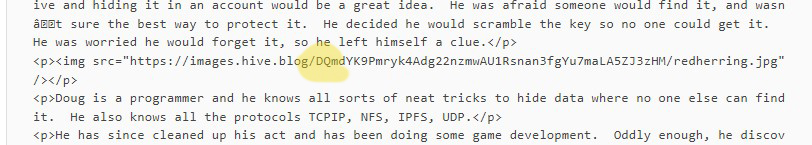
However, we know most IPFS start with a hash of "Qm...", but this seemed different.
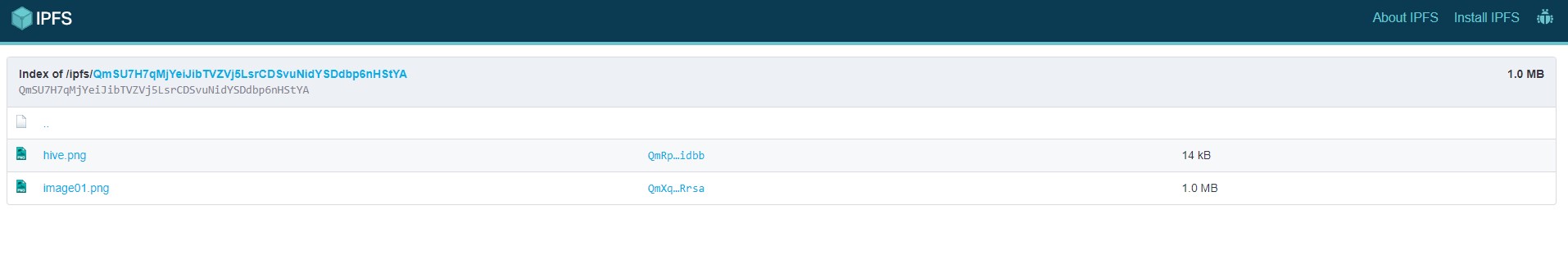
So we decided to enter this hash into an IPFS gateway because Doug says he is adept at using IPFS and got: Not one but two images!!! Oh yeah now it is on like Donkey Kong!
Here is the second image:

Steganography To the Rescue!
Ok now we are on to something! Now Doug was pretty braggadocios about knowing how to hide data. In fact he said, "Doug is a programmer and he knows all sorts of neat tricks to hide data where no one else can find it." Well @benjamintaylor told me that steganography is a way used to hide data in other media like text or images. So we decided to load this image into a steganography decoder and we say this:
.png)
You Know What That Means
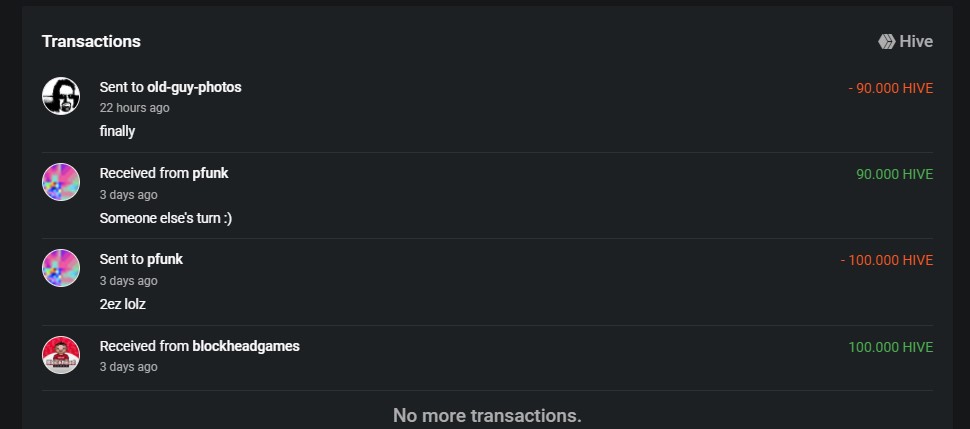
You can see @pfunk made the score first. @benjamintaylor and I would like to say thanks for returning the bulk of the prize to motivate us to keep going on this quest!

Thank You @themarkymark
@benjamintaylor and I would like to express our gratefulness for the time and effort that you put into producing this quest. I have to say we had a wonderful time bonding over this as we worked on our ideas side by side. The time we spend working on this just flew by! The challenge itself was an awesome gift and we much appreciate it. We didn't win a million bucks, but we felt like a million bucks when we won!
Posted with STEMGeeks
Congrats !
That's pretty amazing.
Of course, not the type of challenge for a regular Jane.
I know I learned a lot. Being that my company came over Sunday, it was a perfect way to spend Christmas to be honest. We really had a good time.
Well done!
Congrats!
Thanks so much!! 🙂
lololollololooolll. 🤣
Great job. Awww man... 90 hive? Does feel like a million bucks. ❤️
It felt great to solve the puzzle!
Congratulations @benjamintaylor and @old-guy-photos! You earned the bragging rights!
Sounds like a great bonding experience!
It really was. I knew all those hours he spends
playing video gameshackinglearning on his computer would pay off lol.Ha that's bloody awesome!! Will done the old-guy-photos team!!
Thanks Boom. I guess I got to pay the little bugger some of the loot lol!
Congratulations, super sleuths!🔎🕵️♂️🔍
You and @benjamintaylor had a very Merry Christmas! @old-guy-photos🎅🎄🎁
Merry Christmas & a Happy (and less dystopian) New Year! 🎄🎁 ❤️🙏 Both of ya ate some of my favorites here 🙌.
Ate 🤣. I hope not! I’ll leave that typo alone though🙃. Man I really think the 2020’s are just getting started unfortunately. But let’s see what happens. Much love to you both! & to u @dswigle ❤️
Let's just leave that typo! :)
I will say that we should just see what happens. I am hoping for better! Thank you! Love right back at you! 💙 What does that blue heart even mean?
Blue Christmas, Blue Monday... its got to be a sad heart I would guess?
Nooo. Do I look sad to you?
Well apparently I am wrong as I just consulted the bible and it says:
https://www.cosmopolitan.com/sex-love/a28635219/heart-emoji-meanings/
As usual the OldGuy has no idea whatsoever about any of this stuff and should just be ornery 🙂
I sent a red heart. Get ur eyes 👀 checked @dswigle 🤣. Kidding kidding ☺️ It was in the 70’s there? Here just a few hours north it was 50 tops for under a hour or so. We got snow the morning of the 24th. Just a half an inch but a white Christmas Eve it was. Hmm I’m trying to think of how I can incorporate the twilight zone viewing into a post here. Review? Reaction watch? Maybe talk about a fav episode and how it compares to current events? Ashlees birthday is Jan 1st and she wants to watch a bunch of the marathon. It’s my favorite TV show ever! I’m begging her to open a hive account. I think she’s self conscious about it but I’ve convinced her to at least do a test run post here on my account. Hoping the feedback encourages her 😃. Hmm perhaps there is a idea to mix with the viewing and her art of it 🤔 Cheers to you both 🍻 @dswigle @old-guy-photos
Oh the Twilight Zone episodes are classics. So many good ones. William Shatner as the passenger with the gremlin on the wing freaked my son out for ages! The Billy Mummy one where he wishes the townspeople into the corn...Oh and Burgess Meredith where he breaks his glasses after the nukes....so good!
Into corn? 😁 well Into the cornfield! Turned that one guy who just wanted to play his Perry Como record on his birthday into a Jack in the box! A Jack In the Box with the same old head!
He’s great in that! other two he’s in are good ones also. The one where his grandma calls him from the grave , then the one where his dads Played by Jack Klugman. It’s called “In Praise Of Pip”.
The grandma calling from grave is called “ Long Distance Call”.
https://m.imdb.com/title/tt0734579/
https://en.m.wikipedia.org/wiki/Long_Distance_Call
I will have to check those out. I thought he was a great actor. Of course before your time, but I grew up with him on one of my favorite TV shows, Lost in Space, as Will Robinson 🙂 Even now I want that robot!!! 😁
You know Robbie the Robot was also in two twilight zones? Same model anyway. Hey I’ve posted these before but just in case. My wall below (Anthany Freemont on right)

Oh yeah. Very cool. Thanks for sharing that!
I am just checking my mentions! Oh, I have missed another @geneeverett one!!!
Did Ashely run a test one? I am not to late to see it!!!!1
I like to think I am an optimistic realist. I kind of hope for the best, but I am cautious at the same time.
Ha the only thing I ate was too much fruitcake LOL🤣
You should be ashamed. The Fruitcake lovers of the world look down on you for eating Claxton. I am totally going to have to teach you how to make real fruitcake.
Come to think of it, this is probably has been employed all along because I didn't send you fruitcake. You keep dancing out that Claxton stuff, thinking I'm going to feel bad for you because you had to eat it. I'm just kidding you. I know a lot of people like it. I have to think that's because they have never had good fruit cake. LOL
Well, one makes do with what one has 😳
This has no reason to ever exist.
LOL how can you not like cake, fruit, and nuts?!? So yummy! 😄
Ohhhhhh! Cheater! 😉
You know you want some of that! 😁
NEVER!
Looks Absolutely ummm delicious……. Yea sure 🙃
Oh man you are missing out! Hey just send any extra fruitcakes my way. No worries at all LOL
If I get one like this I’ll indeed send it ur way 😁
No! No! He buys cheaters! I make real fruit cake. Don't let him coerce you into Walmart-made fruitcake!
🤣🤣🤣 no way I was eating a Walmart sponge looking thing 😁. I’d love to try urs though ☺️
Well, I think it's better than @old-guy-photos claxton fruit cake. Maybe. Ill have to ask him. He might be a claxton fan.
Claxton Fan , sounds like the fan of a European Football Team ⚽️ 🤗. Claxton football club. Has a ring to it :)
It does, doesn't it? Oh, you are still up ? When do you sleep again?
Me and Ashlee stayed up till 4am then fell asleep at dinner time🤣. I slept 6.5 hours and woke up right when I responded last two hours. Not the usual but yea now she’s asleep snd I’m up. I think I’ll stay up then crash tonight. I’ll get it down after New Year’s Day
But in general I’ve been sleeping more last couple weeks. We just had some edibles and it threw us off the day before. After our Twilight zone marathon New Year’s Eve & day we’ll get back on a normal track🙌
Haha... Normal, whatever that is.
Thanks for adding value to my votes @investegg much appreciated 🙏
It was a really fun way to spend the day albeit a bit untraditional; it works for us lol. I hope your Christmas was bright and of course wishing you and yours the very best in the New Year Nina!
Congrats and well done :D