Step by step guide to associate a domain or sub domain to your Hive node using Caddy
Note: Keeping your Hive witness server protected is very important. If you want to run an RPC node or expose your RPC node to the public, it is recommended to run it in a separate box and not combine it with your witness server. Having an intermediate Cloudfare tunnel to your server from the DNS is also safe if you enable RPC and expose it for public use.
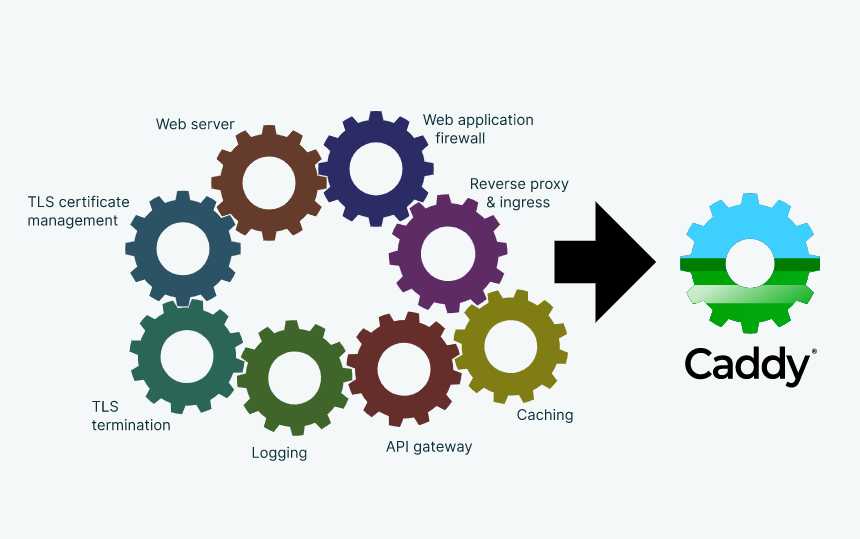
Associating a domain or subdomain with your Hive node is very simple. People who would like to keep their hive node public can make use of this guide and associate it with a domain or a subdomain. In this guide, I will be using CADDY as my web server. There are many advantages to using CADDY as the web server though there are alternative options available. Below are the primary reasons why I choose CADDY over others.
- The commands are simple and easy to use.
- Caddy takes care of SSL certificates by itself for free. No manual setup is required.
The second point is the main reason why I wanted to explore CADDY and have been using it for years now. Now let's get to the topic. I have written similar articles in the past for domain associations. This article is also going to be similarly targeting the Hive node.
Step 1: Install Caddy on the server
The steps are very simple to install Caddy on the server. If you are using an NGINX instance already, you can stop it and then install Caddy. If you are starting fresh, you can straight away go and install Caddy. Below are the commands to get started. All my servers are Ubuntu 20.4 and this worked well for me and I'm sure this should work on other versions of Linux as well.
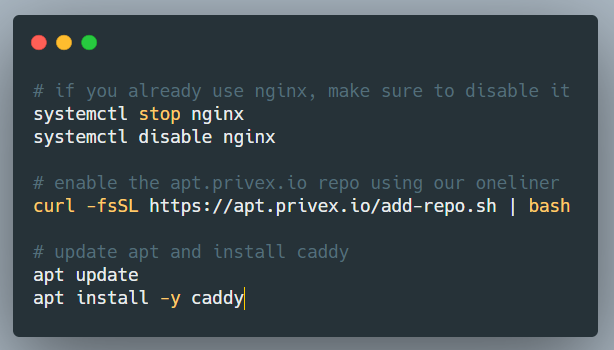
curl -fsSL https://apt.privex.io/add-repo.sh | bash
apt update
apt install -y caddy
I was using a Virtual machine box from @privex so I used their repo to get the package. You can also use a different package link to the repo. The steps are very simple.
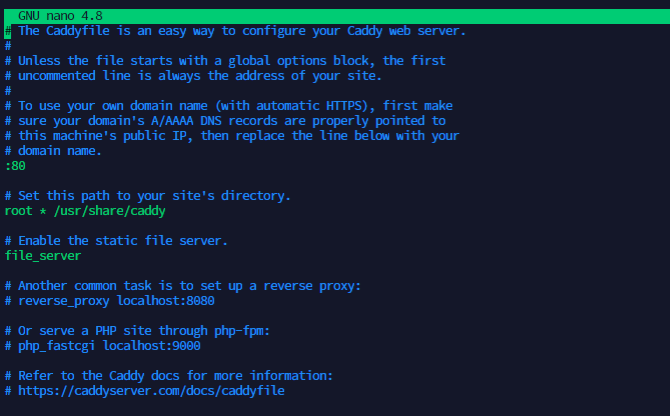
Step 2: Edit the Caddyfile
Caddyfile is the configuration file that has all the information about the sites we are hosting. It is one place where we do all the configurations required for the domain association. The below command can be used to access the Cadyfile
sudo nano /etc/caddy/Caddyfile
The default caddy file contents look like the below:
Once the file is opened, you can make changes in such a way that domain\subdomain is set. I commented out all the existing lines in the file and just added the reverse_proxy line alone. You can also remove all the existing contents of the file and just have the active content alone. That also works. My final Caddy file looked similar to the one below.
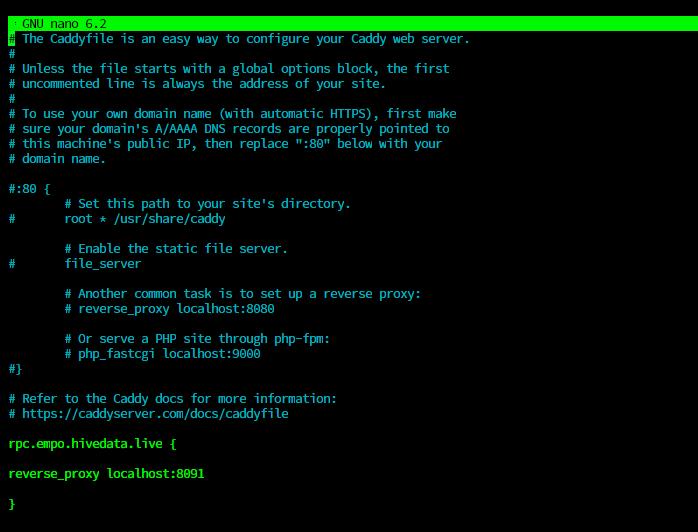
The default http port for a Hive node is 8091. Before we update the caddy file, we have to make sure the config.ini file of the hive node is configured properly to hold the right values. It should have the below value set.
webserver-http-endpoint = 0.0.0.0:8091
If the Hive node is already running it should be running on port 8091. It can be tested with the below commands. Before running this command, make sure the condenser_api plugin is enabled on your hive node or not. Otherwise, the below command will not give the desired output.
curl -s --data '{"JSON-RPC":"2.0", "method":"condenser_api.get_account_count", "params":[], "id":1}' [http://0.0.0.0:8091](http://0.0.0.0:8091)
The output from the above command should be similar to the below:
{"jsonrpc":"2.0","result":2443531,"id":1}
If you are using Docker, it may not be 0.0.0.0 but docker's IP address. You can find the docker's IP adress and use it instead. The above configuration in the caddy file means that all the requests reaching rpc.empo.hivedata.live will be directed to 0.0.0.0:8091 which is the 8091 port in localhost. rpc.empo is the subdomain I'm using in this configuration. If you want, you can also use a domain directly.
Step 3: Enable your Caddy service
You can either go to the directory of the Caddyfile and run the service manually with the below command.
caddy run
Or enable it as a service. In my case, I enabled it as a service with the below commands.
systemctl enable caddy
systemctl status caddy
systemctl restart caddy
The status check command will tell you if the service is running fine or not. In some cases if the configuration is incorrect or if there are unwanted characters in the Caddyfile, the service may fail to run. The status command will show you an active (running) status similar to the one below.
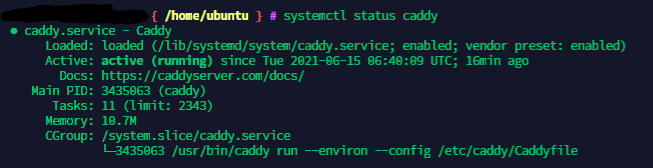
Sometimes the caddy service would be already running on your machine and you may not need to start it again. Only if you are making changes to the Caddy file, do we have to restart the service for the changes to take effect. Otherwise, we are good.
Step 4: Point your domain to the IP address of the server
This is the last step to completing your setup. We have to point the domain\subdomain to the IP address of the server so that all the requests coming to the domain are redirected to the server and caddy is able to serve those requests.
In my case, I have my domains on Namecheap and as I was adding a subdomain, it was very simple to just add an A record in the domain's DNS configuration and point it to the IP address of my hive server.
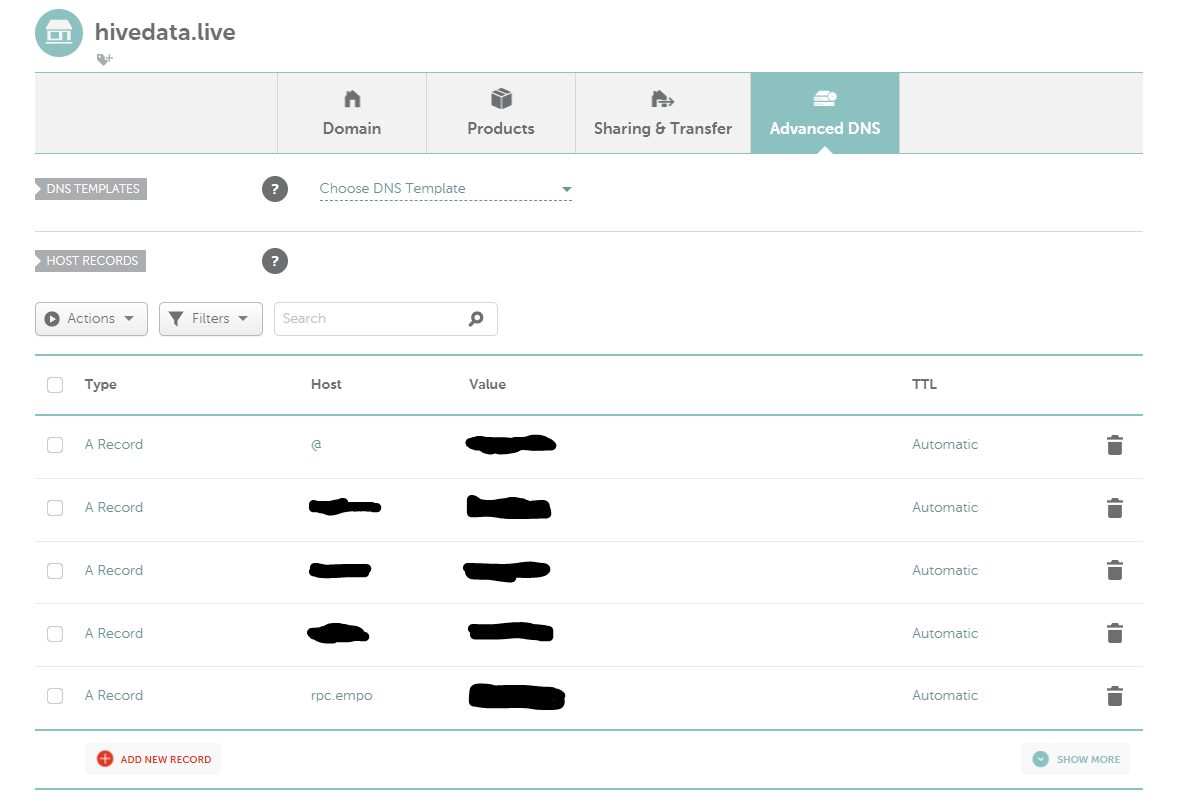
The configuration page looks similar to the above and it will vary from one service provider to another. In the Value field, you will have to enter the IP address of your Hive node. In our case, you can see an entry for rpc.empo.
You can do this step before all the other steps as well. It doesn't really matter if you add the A record before or after. It is good to do it before because it usually takes some time for the domain to propagate. If you do this step first, the propagation would have happened before you complete the other steps.
Step 5: Test if our configuration worked
It is quite simple to test if the configuration worked or not. Try visiting your node URL directly from a browser. In my case, it is https://rpc.empo.hivedata.live/. The URL worked. It should give you a result similar to the one below.
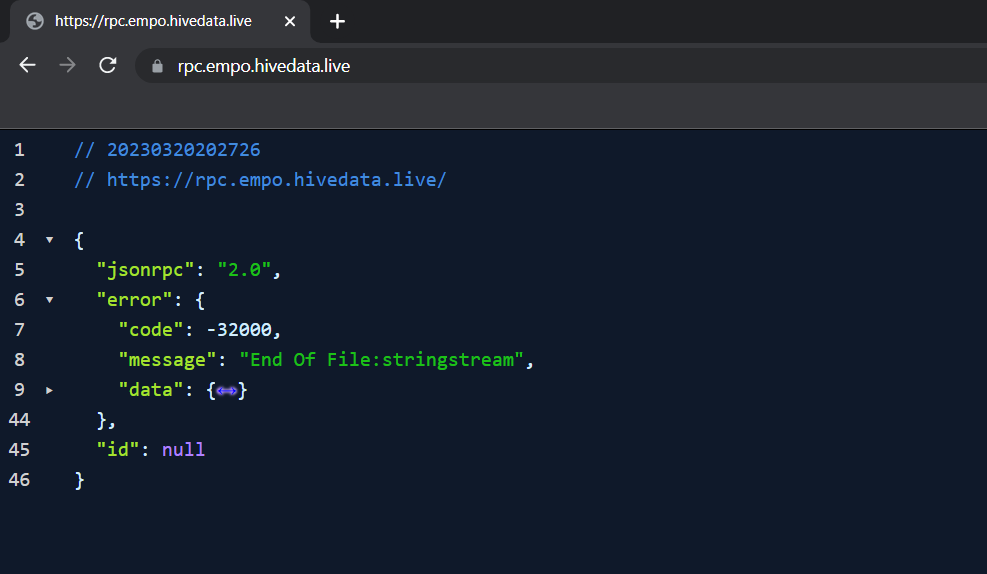
You can also test this on your Linux machine using the CURL command. The output should look like the one below.
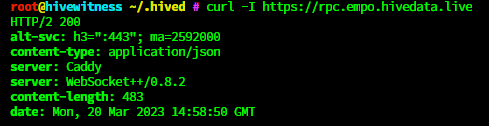
We are done with the domain association. You can share your rpc node URL with others and make it public. The good thing about CADDY is that we don't have to do an SSL setup. It will be automatically taken care.
Note: This article will have contents repeated from my previous blogs as some of the steps in this guide are the same for other guides as well.
If you like what I'm doing on Hive, you can vote me as a witness with the links below.
 |
 |
 |
 |
 |
 |
I highly recommend not making a witness node public or exposing anything more than an SSH port to get into it.
Is it okay to then have a Cloudflare layer in between to not expose the server directly?
If you mean cloudflare tunnel, then yes as that keeps it private. But there really isn't any reason I can think of to expose anything other than SSH. Witness nodes are the backbone of the chain, and they should be protected as much as possible.
$WINE
Congratulations, @theguruasia You Successfully Shared 0.800 WINEX With @balaz.
You Earned 0.800 WINEX As Curation Reward.
You Utilized 4/4 Successful Calls.
Contact Us : WINEX Token Discord Channel
WINEX Current Market Price : 0.150
Swap Your Hive <=> Swap.Hive With Industry Lowest Fee (0.1%) : Click This Link
Read Latest Updates Or Contact Us
This post has been manually curated by @bhattg from Indiaunited community. Join us on our Discord Server.
Do you know that you can earn a passive income by delegating to @indiaunited. We share more than 100 % of the curation rewards with the delegators in the form of IUC tokens. HP delegators and IUC token holders also get upto 20% additional vote weight.
Here are some handy links for delegations: 100HP, 250HP, 500HP, 1000HP.
100% of the rewards from this comment goes to the curator for their manual curation efforts. Please encourage the curator @bhattg by upvoting this comment and support the community by voting the posts made by @indiaunited.
Congratulations @balaz! You have completed the following achievement on the Hive blockchain And have been rewarded with New badge(s)
Your next target is to reach 3750 upvotes.
You can view your badges on your board and compare yourself to others in the Ranking
If you no longer want to receive notifications, reply to this comment with the word
STOPCheck out our last posts:
Support the HiveBuzz project. Vote for our proposal!