Gridcoin PSA - Check your wallet security!

Overview
So recently there have been cases where Gridcoin has been stolen from members of the community. There have only been two cases that are official so far and I want to go in depth on how to keep your computer safe and simply document these events in case my information may be helpful in the future. If you have any information about the transactions or have ever dealt with any addresses that are featured here, your information is valuable and comments here are well appreciated. If there is any new information comes in, I will update it accordingly.
Case 1: 70k GRC stolen 6th of February 2019
Transaction ID: 7bd3b716bb69cb201f03875d5f8eccebd5fc801f21660ad83f582f1cb507d9ee (view on block explorer)
Offender's address: S997pMdQ7L9KyjXQUsaZyXjVxYEscGxdht (view on block explorer)
Timeline of transactions
- 6th Feb - Offender transferred GRC to their wallet. This has a high chance of being an exchange wallet given it has only one output (with all funds) and outputs to another high chance exchange wallet and a regular user.
- 14th Mar - TX out of wallet occurred
S7yqiY9AaenNKwAPvF8QbzNWCYXgEQeUpT - 29.1k GRC
SGEAXhp9iSWWjTF95nWudfzx2BvxFmMLgk - 40.8k GRC
As for the S7 address, this seems to be an exchange wallet. This is because the transaction chain goes on and on, spending only small chunks to crunchers and investors.
The SGE address is a little bit more interesting, it (as of posting this) contains 85.5k GRC in an investor wallet which has not staked ever but has transactions dating back years. It is likely that this person was a buyer from an exchange that listed GRC at the time.
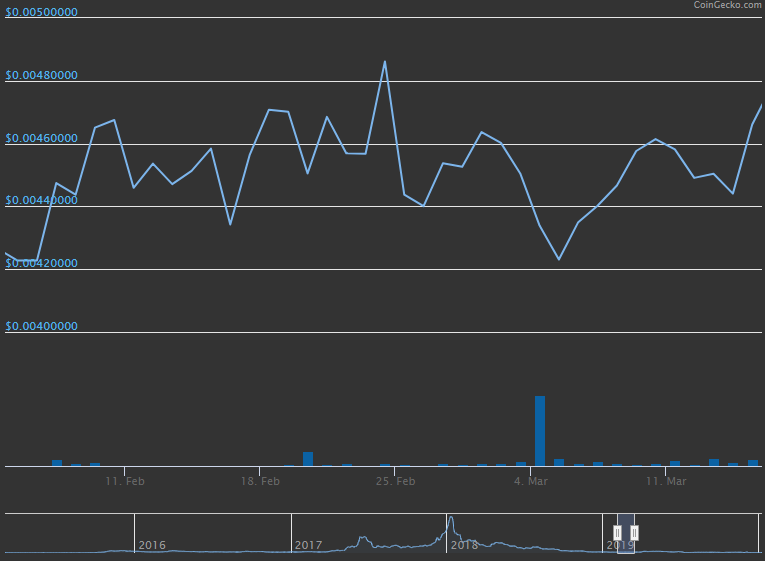
Price action during this period does not provide any additional information considering an increase of only 0.0004 USD. Therefore we cannot make any conclusions on the reason for the delay between transactions 1 and 2.
Brief description of the cause
- Wallet left fully unlocked
- VNC (remote desktop) software was running and open publicly
Case 2: 522k GRC stolen January 2nd 2020
Transaction ID: 4396a95cf0a0a906b939e1e4851803ae5dd0cca68ee979426c154f0123d33ada (view on block explorer)
Offender's addresses:
SE5Ry6eSzs5tifV5qFfMWVn9wfZRHhzGhe (view on block explorer)
S9531rB4TzcAfevud15AbWEzUvGLpaMant (view on block explorer)
Offender's IP address was logged, geoIP indicates that it originates from the Netherlands.
Timeline of transactions
- 2nd Jan - Offender transferred GRC to their wallet.
- 5th Jan - Offender staked. Unlucky that the wallet is not tied to a CPID.
- 5th Jan - Offender spent the staked GRC (transaction)
- 5th Jan - Offender spent 2 of the 10 staked GRC (transaction, related address:
SLo9arnZaQiAnvjsdoQ7WAuoGcRit7yYQg)
The interesting thing with this case is that none of the addresses appear to be exchange addresses. For the future, studying the actions of the address in action 4 might yield some interesting information if the offender decides to move such funds.
Brief description of cause
- Wallet was thought to have been unlocked for staking only (no confirmation if it was unlocked fully)
- Remote desktop software was running on the user's machine
How to keep yourself safe
It is clear from these experiences that Remote Desktop Protocols (RDP) and related software have been to blame. This is software that allows you to remotely connect to your computer over the internet. Some examples include VNC, Teamviewer and Google's Chrome Remote Desktop.
So the key concept to learn from here is to never store Gridcoins (or cryptocurrency) on the same computer with RDP enabled.
Here is a video I made describing how to keep your Gridcoin wallet secure...

The following are some basic security steps, most of which are also mentioned in the video:
- ALWAYS keep your wallet open for STAKING ONLY. This is an option whenever you click the unlock button for your wallet. Make sure the box is always checked. This ensures that you can still stake but your funds cannot move from your addresses. If you have to set your wallet to fully unlocked for any reason, make sure you switch it back soon and not leave it unattended.
- Choose a strong password at least 10 characters long. The longer and more complex the password, the less of a chance a brute-force attack can be successful.
- Backup your wallets and config regularly onto at least one other device. This reduces your chance of losing your funds from loss or damage on a physical level. To backup your Gridcoin wallet click
File > Backup wallet/config... - Don't store large amounts of funds on a computer you use every day. This computer being used daily is more susceptible to viruses and unexpected damage.
Stay safe out there!
It is also worth noting that with the new side staking features, users can create a "hot and cold" wallet setup for themselves. In this kind of situation the user can keep a majority of their coins offline ("cold") on a wallet that is rarely used, and have a smaller wallet that is kept online 24/7 ("hot") that side stakes a portion or all of its proceeds to the cold wallet. This allows you to stake at a reasonable rate without the risk of keeping all your coins in one online wallet.
If you need remote access to the machine with the wallet, then please ensure that SSH, RDP, and/or VNC are behind a firewall and use a VPN connection to get to them, rather than exposing the services directly. This requires a firewall, or internal machine that supports VPN software. (If you use a machine internal to your network for VPN, you port forward the VPN port(s) (ONLY!) to your internet address.)
None of these three services should be exposed to the outside directly on the Internet unless ABSOLUTELY necessary, and if they are, I would not host a wallet on them at all.
It is a good idea if you need SSH exposed directly on the internet to use an extremely strong passsword, and/or certificate based authentication. I would also limit the IP range of accepted connections to that service if your access is from known IP range(s).
It is also a bad idea to use cloud-based third-party remote access services.
For anyone running a server, here's a SSH certificate authentication tutorial. I personally think that everyone with public facing ssh should do it.